Business Process Management Software
Process Management
Complete management of debts according to Strategy, Workflow and Standard Operational Procedures (SOP) configured in particular for each client.
Legal Management
Complete legal management of all of the court cases related to processes management, including all documentation, and all of the Meta data requested by clients.
asset Management
Extensive asset management system that permits storage and management of all of the assets related to processes management, including all of the documentations, financial status and tasks related to assets.
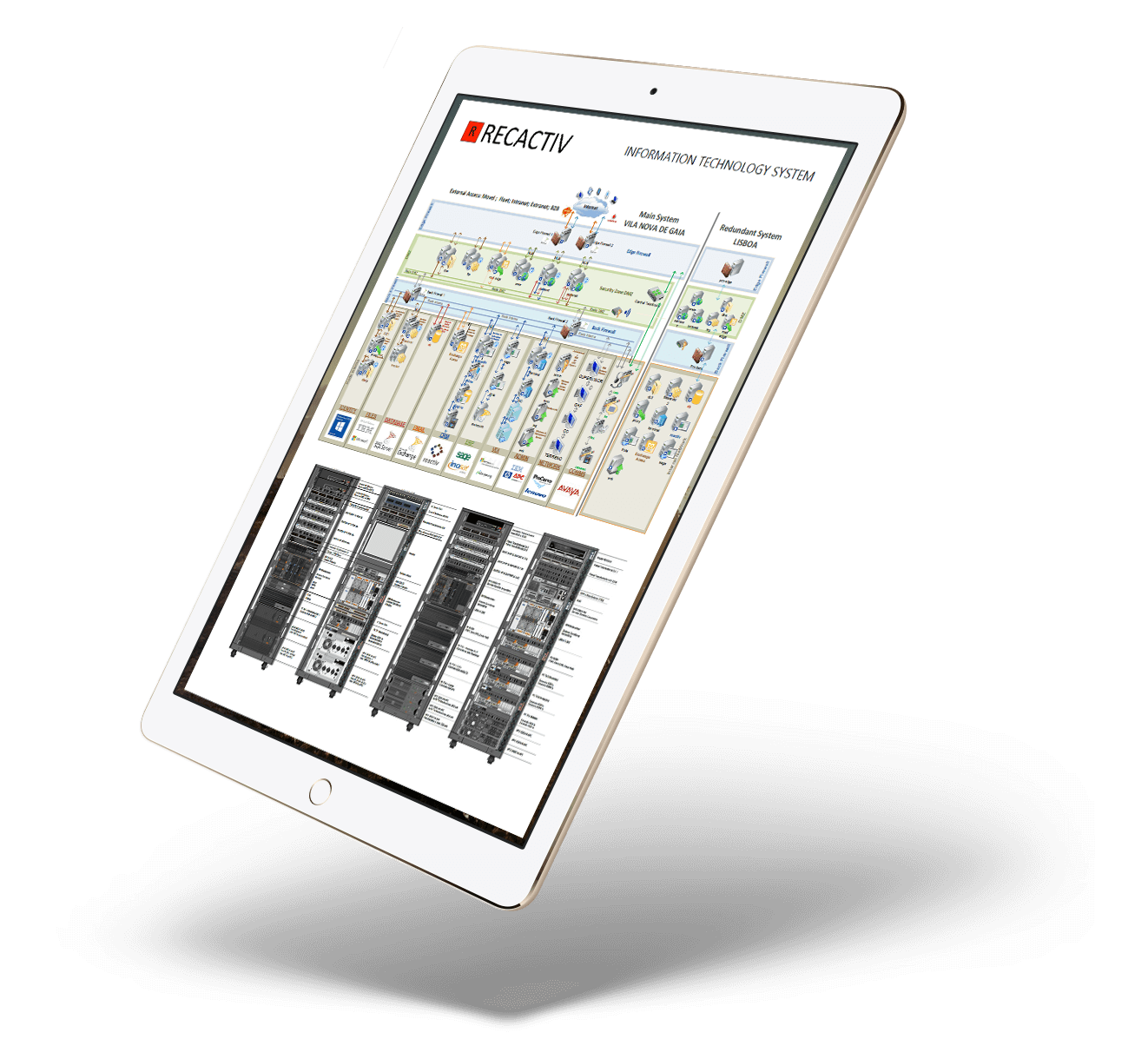
Recactiv datacenters
Recactiv Datacenters are based on a private cloud infrastructure that exists on 3 physically different places for optimum redundancy and avaiability.
Memory
/Gigabytes
CPU Cores
/CPU Cores
Storage
/Terabytes
Servers
/blade servers
Secured Remote Access Services
RECATIV offers a wide range of services accessible remotely, all with extensive security.
Extranet
RECACTIV Extranet is a tool that our clients uses to review the processes they handled to us:
Intranet
RECACTIV Intranet is a tool to our internal users to manage different parts of their work.
Remote Desktop
RECACTIV Remote Desktop is a tool to our internal users. This tool is accessible using HTTPS from computers, tablets and smartphones on remote locations.
Secured File Server
RECACTIV Secure File server is a tool that our employees and clients uses to securely share files.
VPN
Restricted information must only be accessible via VPN witch require multi-factor authentication.
Secured Email Server
RECACTIV Email Server is a tool used by all our employees. This tool is accessible using HTTPS from computers, tablets and smartphones on remote locations
Information Security Management System
The goal of Recactiv Security management system is to provide to all our clients and stakeholders an IT system that has a high level of security.
Recactiv has a security policy that was made taking in consideration all the aspects of the ISO/IEC 27002 that complies with international standards, incorporating generally accepted good security practices
Definition
In information security, confidentiality "is the property, that information is not made available or disclosed to unauthorized individuals, entities, or processes.Recactiv Goal
Minimize confidentially risks , with a target of 100% confidentialityRecactiv Controls
The confidentiality of the information is always protected from non-authorized access, using a multitude of controls, like multiple firewalls, security certificates, encription, etcDefinition
In information security, data integrity means maintaining and assuring the accuracy and completeness of stored and processed data over its entire lifecycle.Recactiv Goal
No failures in missing data, with a target 100% integrityRecactiv Controls
The integrity of the information is assured by diverse security controls, including access control, database and file replicas, backups, anti-malware, etc.Definition
For any information system to serve its purpose, information must be available when it is needed. Including means the computing systems used to store and process the information, the security controls used to protect it, and the communication channels used to access it.Recactiv Goal
Excellent System uptime with a target of 99% availabilityRecactiv Controls
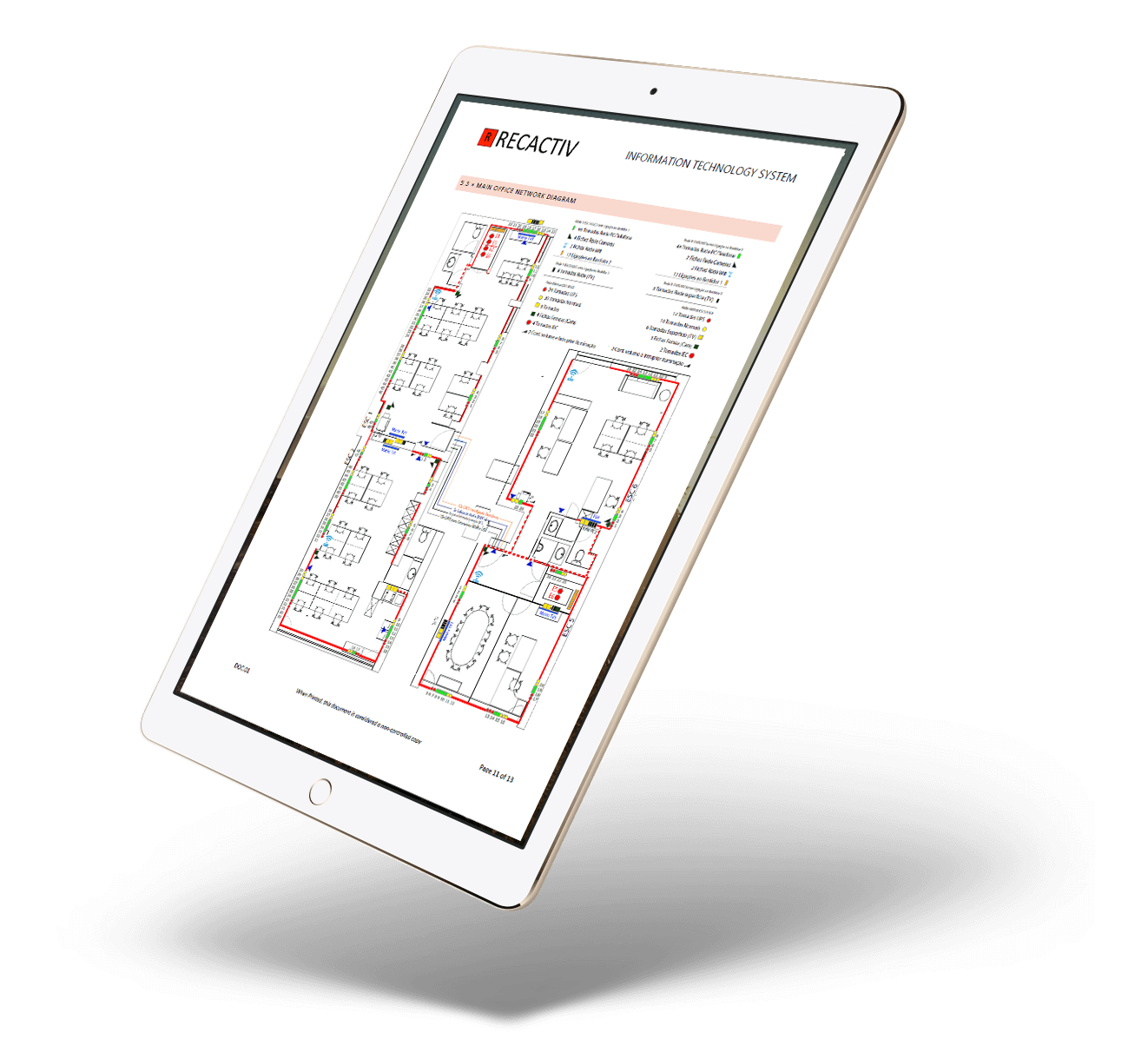
Redundant datacenters, so we keep working if anyhing fails, with a clear plan defined in a Business Continuity Plan that we test every year.Recactiv Network
Reduntant Internet Access
Recactiv maintains a highly available internet connection in all of our sites. The main High Speed 500/500Mb Connection is backed up automatically using a 4G connection
Communications System
A Communications System with unified voice and data, allows full integration with management software. Includes 60 simultaneous and extendable voice channels.
Corporate TV
Recactiv mantains a complete corporate TV system. In every room where we display online results of the team, provided by multiple software wallboards.